Dovestech Selected for Proof of Concept Development
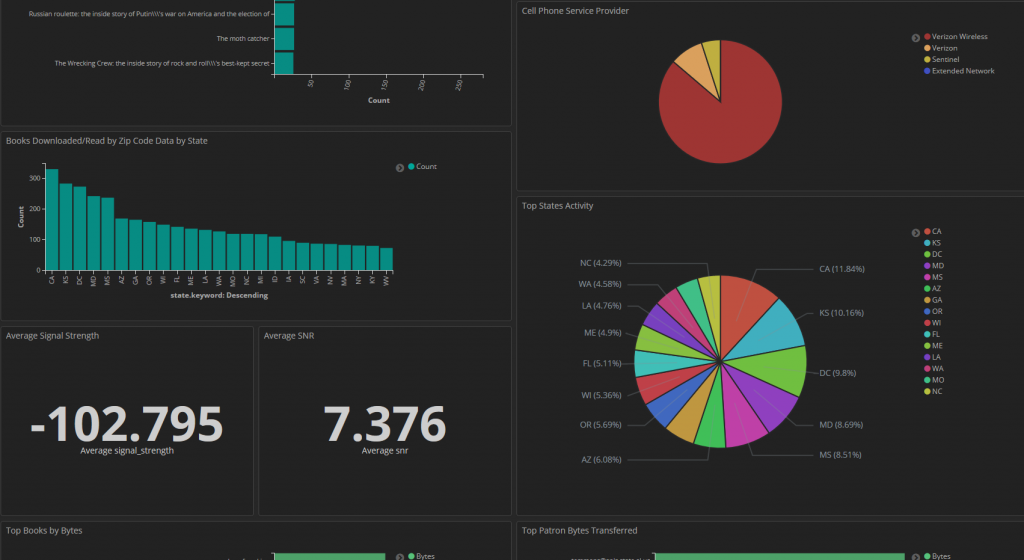
Dovestech recently was selected to exhibit our expertise and knowledge of data science for IoT analytics for a government customer. The customer sought out firms that indicated they had expertise in data analytic and visualization using ElasticSearch. Guess what? We were down selected as the top firm and we are off to the races building […]
Maryland Cyber Security Non-Profit Pushes Community Innovation and Collaboration

Maryland Cyber Security experts are growing excited about a new cyber security non-profit which is taking aim at bringing the community together for a larger impact. Maryland Innovation & Security Institute (MISI) is a non-profit formed exclusively to further and promote charitable, educational, and scientific purposes including, but not limited to, furthering innovation in cybersecurity […]
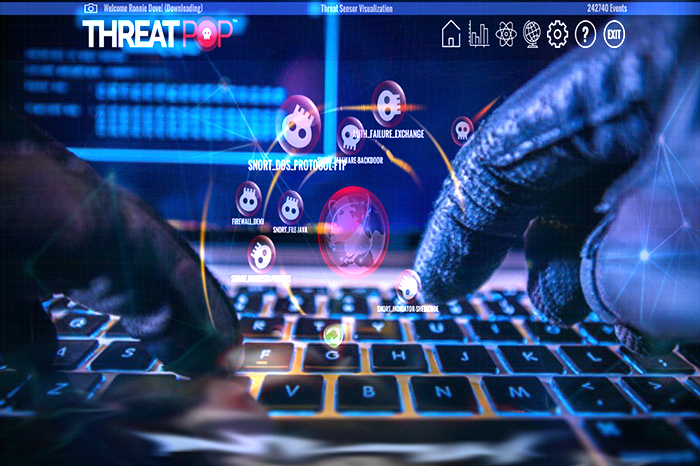
Game Engine Technology for the Enterprise

Game engine technology isn’t only for games anymore. Businesses are often seeking the best visualization and the most memorable interactive experience for customers and employees. Dovestech has been leading the charge when it comes to gamification for the enterprise, releasing its state of the art cyber security visualization product known as ThreatPop. The product offers […]
Inside the Lab: User and Entity Behavior Analytics

Members of our team have been studying existing technologies being applied in our customer environments for what is known today as User and Entity Behavior Analytics (UEBA). We have been engaged in examining the current sate of the market and studying the benefits and features claimed by new entrants into the market place. Legacy SEIM […]
Dovestech Adds DoD Subcontracts

We are excited to add a subcontract that will see us supporting the Department of Defense and that will allow us to contribute to our nation’s critical security needs over the next five(5) years. We will be applying expertise in cyber, data science, systems engineering and applying some advanced technologies to develop state of the […]
Dovestech’s Managing Director Delivers Commencement Speech

Dovestech’s Managing Director, Armando Seay, and Dovestech’s CTO, Ronnie Dove attended NPower’s graduation ceremony where Armando Seay gave an incredible commencement speech to the graduates. NPower creates pathways to economic prosperity by launching digital careers for military veterans and young adults from under-served communities.
Dovestech Explains: GPU Processing Power vs Passwords
Have you ever wondered how hackers are able to make quick work of leaked password databases even if the passwords are hashed? First we must discuss the basics of what a hashed password means. Cryptographic hash functions are a way to turn a text representation of data into a fixed-length “fingerprint” based on the protected […]